Industrial Cybersecurity Solutions
Protect your Operational Infrastructure
Belden’s broad portfolio of industrial cybersecurity solutions offers visibility to & protection from events that threaten the safety, quality & productivity of your control systems. From hardware devices with embedded security features to cyber- resilient software, we help customers transform raw system data into actionable insights for a powerful defense against cyber disruptions of any kind.
-
Cyber Solutions
-
Network Security & IT/OT Convergence
-
Trends & Data
End-to-End Cybersecurity Solutions
Explore the industry’s broadest portfolio of industrial hardware & software solutions designed for maximum uptime, safety & infrastructure compliance–all from one vendor with the brands to improve your security posture.
-
Firewall Solutions
-
Network Software
Core-to-Edge Firewall Solutions for OT Environments
EAGLE40 Industrial Network Firewall Security

- Heightened performance & security including more port options with increased bandwidth & encryption capabilities
- Easy configuration with streamlined user interface, firewall learning mode & deep packet inspection (DPI) modules for all skill levels
- Convection-cooled metal housing for 24/7 network monitoring
EAGLE One Security Bridge & Router

- Combine Stateful Packet Inspection (SPI) for bridged or routed communications with unique Firewall Learning Mode
- Add safe, cost-effective protection to your industrial automation network
- Build redundant backbone network connections for production cells combined with comprehensive Network Address Translation (NAT) techniques
EAGLE 20/EAGLE 30 Industrial Firewalls with HiSecOS Software

- Use Stateful Packet Inspection (SPI) firewalling & optional Deep Packet Inspection (DPI) for routed communication to secure industrial networks
- Build connections with two optional SHDSL ports & up to 6 LAN ports (2 Gigabit ports)
- Easy deployment with one-click rule setup via Firewall Learning Mode
- Maximum uptime via redundancy protocols including virtual router redundancy (VRRP)
Tofino Xenon Security Appliance with DPI

- Industrial Layer 2 firewall with stateful & deep packet inspection (DPI) for bridged communication protects PLCs, RTUs & other control devices
- Simplified installation with zero-impact plug-n-protect technology, requires no pre-configuration, network changes or control system disruption
- Deep protocol awareness without required vulnerability updates with 'Configure-Test-Deploy'
Network Management Software
Hirschmann Industrial HiVision Software

- Safe automatic identification of all network devices with automatic topology detection
- MultiConfig™ for simultaneous configuration of multiple devices
- Instant visibility of key performance indicators & hardware security conformance through network dashboard
- Improved uptime & security with quick fault-finding & timely remediation
Network Security & IT/OT Convergence
Who Owns Industrial Cyber Protection?
"…reliance on control systems continues to expand across not only industrial settings, but also the operation & maintenance of our cities, our buildings and all kinds of modern smart applications. The convergence of IT and operational technology (OT) has now come into popular awareness as the lines between the Internet of Things (IoT) and the Industrial Internet of Things (IIoT) have blurred and the media have given increased coverage to security breaches and their impacts."
2017 SANS Survey: Securing Industrial Control Systems, Executive Summary
IT vs. OT—What’s the Difference?
Traditionally, industrial enterprises have kept everything separate with information technology professionals managing the office network—an mild environment where internet speed & data security were paramount. On the plant floor, operational technology professionals addressed harsh environmental conditions with a closed air-gapped network & & focus on keeping
production running safely.
For more, read Why IT-OT Convergence Means Greater Resources for Both.
| IT Priorities | OT Priorities |
|---|---|
| Confidentiality | Safety |
| Integrity | Availability |
| Availabilities | Integrity |
| Confidentiality |
Katherine Brocklehurst, “Cyberattacks and Bottom Lines: Who Has Responsibility for Industrial Cyber Risks?” Advancing Automation eBook, Vol. III:20-25.
Secure. Reliable. Resilient.
Ensuring a secure and reliable industrial infrastructure in light of new cybersecurity threats.

Today's Picture—A Single Converged Network
Now, more devices on the plant floor need to be connected to the Internet. Remote locations must be managed from one central location. Executives in the office demand data to manage plant maintenance, upgrades, output quantity and quality and inventory levels.
That means blurry – or nonexistent – lines between IT and OT roles and responsibilities. The network of the future will be unified to serve both worlds.
Automation & Data Exchange in Real-World Applications
Merging automation networks of the factory (OT) with the data exchange office network (IT) requires intentional actions. Here are a few steps to get you started.
- Know your assets–including the protocols & languages that run devices
- Open lines of communication so everyone shares common vocabulary of terms—see the blog How Plant Operators Can Overcome the Language Barrier
- Leverage expertise from both IT and OT to re-align priorities—see the blog IT/OT Convergence Means Greater Resources for Both
- Set formal policies for network management, clearly defining converged roles & responsibilities
- Promote ongoing education to learn & adapt best practices
Trends & Data
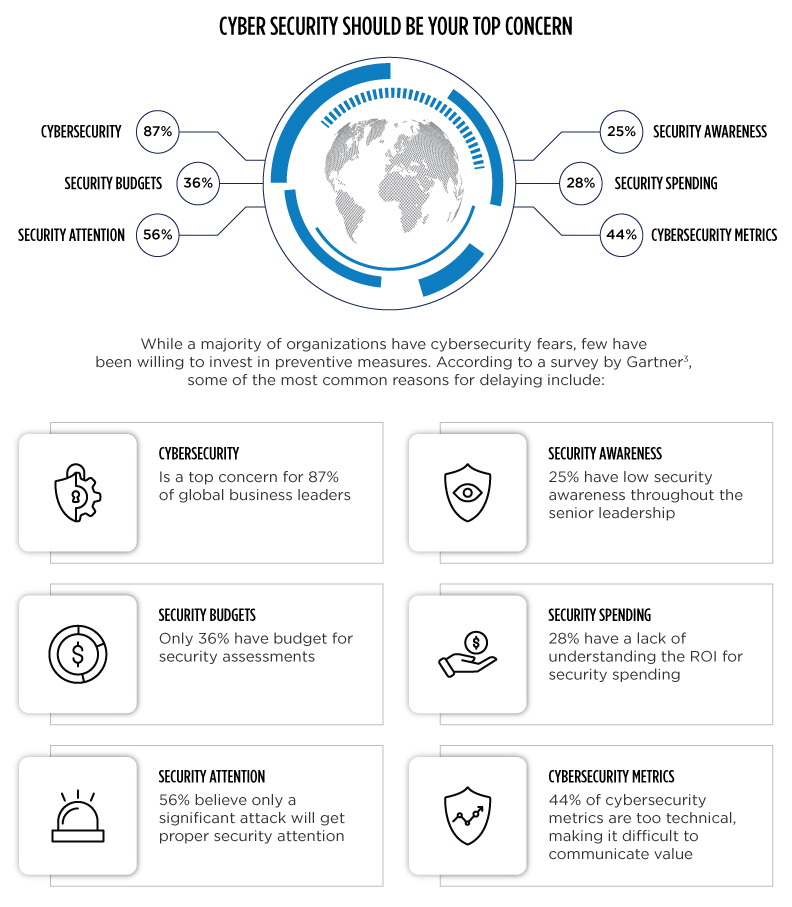
While a majority of organizations have cybersecurity fears, few have been willing to invest in preventive measures. According to a survey by Gartner3, some of the most common reasons for delaying include:
The Cost of Catastrophe
Current data suggests three of four cyber events are due to unintentional human error or accident*
Whether malicious or mistaken, cyber events put worker safety at risk, shut down production, disrupt public utility services & erase profits.
The Lesson?
Start now—with your most critical assets. Start with auditing where you are today & aligning IT & OT protocols.
Enterprises that wait for the "significant" cyber event before they act will find a sobering price tag
| Unintentional Threat | $2M | Excessive network traffic recently caused a major UCA nuclear plant $2M after cooling drive controllers crashed. |
| Accidental Exposure to Malicious Threat | $14M | Exposure to an internet worm shut down 13 auto plants for less than 1 hour, but cost the company $14M. |
| Malicious Intentional Attack | $1T | The Stuxnet virus set Iran's nuclear program back 2 years. A similar attack on the US could cost the government $1T. |
Let's get started
We protect the world’s leading organizations against the most damaging cyberattacks.